WildCAT Wireless Threat Visual Analytics

WildCAT is a turn-key system that helps assure the security of the IEEE 802.11 (“Wi-Fi”) wireless space. The innovative design leverages existing physical security forces to help assure information systems security. It provides a rich visual interface for analyzing wireless networks and supports automated alerting based on risk categories to minimize time and labor costs associated with analysis.
Overview
The innovative WildCAT design leverages existing physical security forces to help assure information systems security. It provides a rich visual interface for analyzing wireless networks and supports automated alerting based on risk categories to minimize time and labor costs associated with analysis.
Our approach outfits existing security/maintenance/delivery vehicles with a small wireless discovery system. This discovery system, which operates whenever the ignition is on, collects 802.11 network data and securely transmits it over a cellular data network to a centralized monitoring and analysis center. There, analysts use automated alerts and a visual analysis software tool to identify suspicious events in the incoming data stream. If an analyst discovers a potential threat, he can send a message to a display inside the patrol vehicle. This allows the physical security force to interdict the threat.
The combination of a persistent physical security force presence with the computer security expertise of remotely located network defenders allows WildCAT to:
- Detect and locate wireless network threats and vulnerabilities
- Assess compliance with defensive network policies (e.g., wireless device ban)
- Respond to wireless network attacks and vulnerabilities
WildCAT was built with support from



Background
Wireless Security Background
Defending and maintaining the operational performance of computer networks is a full-time job. Ensuring continuity of operations and missions relies on the confidentiality, integrity, and availability of networks and the data that traverses them. Yet it is difficult to obtain situational awareness of what’s going on in a computer network. The addition of wireless technologies — especially the inexpensive and pervasive IEEE 802.11 — has further compounded the complexity of this problem.
Wireless technologies have created an additional space that must be monitored: the radio spectrum. With critical capabilities either relying directly on wireless technology, or on resources that are potentially accessible via wireless technology, all organizations must now build capabilities to protect and defend this space.
One of the most prevalent threats to an organization’s security is its own employees; and it can be the most motivated who are the worst offenders. Take, for example, an employee who is frustrated by the slow adoption of wireless by their IT department. All they need to increase their productivity is a simple wireless connection. They think, “What could possibly be the delay — after all, the physical setup for a wireless access point is pretty simple: You take it out of the box, put it on a shelf near a network jack and a power outlet, plug in the power cable, and plug in the network cable!” Unfortunately, this employee self-help creates unmanaged, unmonitored, often ill-configured infiltration points into otherwise secure networks.
With the now ubiquitous presence of wireless hardware in everything from laptops to cell phones, employees don’t need to even do something as obvious as plug in an unauthorized access point to create these infiltration points. Malware or software misconfigurations on employee devices can quietly transform them into access points, bridges, or remote agents. These compromises can lead to theft of data, injection of untrusted data or malware onto a network, and denial of service.
In the same way that all organizations are affected by the need to defend against employee self-help, all organizations should also routinely conduct vulnerability assessments. This includes discovering all nearby wireless devices, investigating rogue devices, and verifying the configuration of access points, clients, and network infrastructure. In order to be effective, it is critical that such assessments be performed routinely. Organization that process credit card data, for example, are required by industry standards to conduct such wireless security audits quarterly.
This need for around-the-clock scanning is one of the primary growth drivers for the wireless intrusion detection/prevention system (WIDS/WIPS) market. Such systems monitor the radio spectrum for the presence of unauthorized, or rogue, network equipment, wireless attacks, and can even monitor the health and performance of the wireless network. In 2010, the market was valued at more than $270M, up from $119M in 2007; it is expected to reach $350M in 2012.
One of the key limitations of all WIDS/WIPS, however, is their range. WIDS and WIPS come in two flavors: embedded and overlay. Embedded systems utilize the access points in a network to perform both defensive and network operations. Overlay systems employ dedicated wireless radios that exclusively perform defensive operations. Both systems, though, require access point hardware to be installed throughout a building or facility; each device costs between $850 and $2,600, installed. Especially for large facilities, this high cost of installation often means that significant areas of a campus or building are left uncovered by WIDS/WIPS sensors.
Compounding this problem, threat actors can employ amplifiers and high gain, directional antennas to breach wireless networks from an increasingly distant range. Detecting and locating these remote attackers presents a significant challenge. And attacks on targets that lie outside WIDS/WIPS sensor coverage will go undetected without supplemental coverage.
One tactic that can be used in response to this more distant threat is to employ specialized personnel to patrol an area with laptops or other portable wireless detection and survey tools. While such an approach satisfies the need, it is costly. Many organizations simply cannot afford the cost of using cyber vulnerability specialists to provide continuous wireless surveillance. This limits the window of time that policy enforcement and threat detection scanning is taking place — increasing the risk of exploitation by an adversary.
Description
System Description
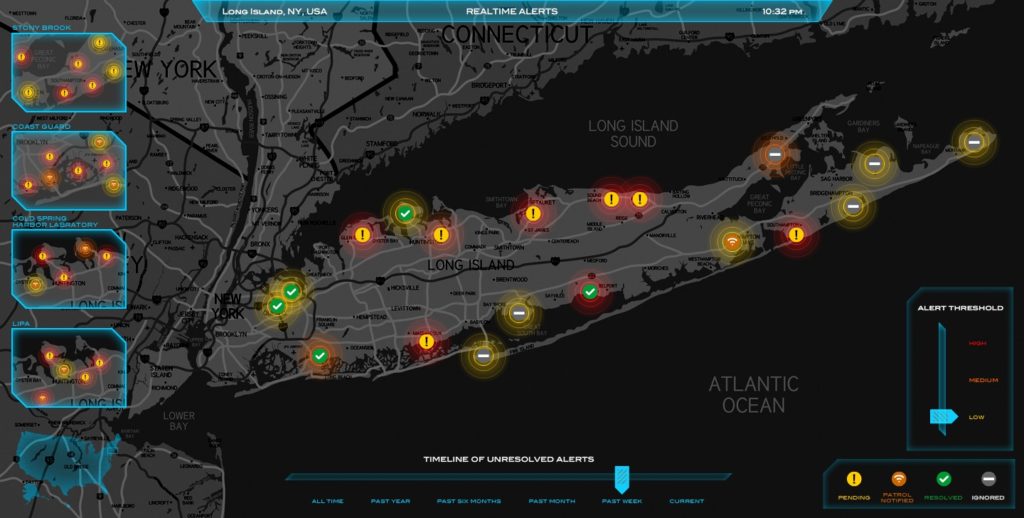
A simplified overview of the WildCAT system is shown below. The two visible components of the system are the “collectors” and the “analysis workstation”. Not shown is server software that receives data from the collector hardware and makes it available to the analysis workstation software.

The ruggedized in-vehicle collector is equipped with an 802.11 network detector, a GPS device, and cellular network connectivity. This collector runs a modified version of the Naval Research Laboratory Flying Squirrel wireless discovery software and also consists of a magnetically mounted, omnidirectional antenna, and an in-vehicle display for showing messages sent by an analyst.
The analysis workstation allows analysts to drill down more deeply into the collected wireless data. The workstation has been designed to support the visual information-seeking mantra of “overview first”, then “zoom and filter”, and “details on-demand”. This approach allows analysts to efficiently sift through large volumes of data and aids detection of suspicious wireless activity.
The workstation is based on the MeerCAT visual analysis system. MeerCAT was originally developed by Secure Decisions for DoD analysis of wireless vulnerabilities, and now has ~1,600 users throughout the DoD, NSA, and private defense contractors. The proven MeerCAT design helps network defenders locate 802.11-based wireless assets and networks to assess their risks using data from tools like Flying Squirrel, Kismet, and NetStumbler. MeerCAT provides a 3D geographic map display of wireless devices, their attributes, and relationships – as well as visual representations that support comparisons over time. Multiple coordinated views support rapid exploration of the data.
Features
Features
Collector installs in any vehicle with a 12V power supply
Collector does not require operator input
Analyst-customizable alert patterns automatically identify suspicious traffic
Click-through, template-based reporting capability
Collector reports data via encrypted cellular link
Supports post-hoc and real-time analysis of the wireless infrastructure
Collector reports data via encrypted cellular link
System collects and aggregates data across multiple locations, vehicles, and times
Visually integrates and correlates data from wireless discovery and security tools with geographic information to quickly locate wireless assets and threats, identify vulnerabilities
Provides interactive geospatial, topological, and spatiotemporal 2D, 3D, and drill-able views
Integrates real-time and historical information to visually capture the dynamic relations and behavior of mobile assets and networks
Facilitates mapping business functions to wireless assets
Analyst can send messages directly to patrol
Advantages
Analysts can figure out how to detect suspicious traffic once and then create an alert pattern to teach the system how to do it, making the system work individually for them
Analysts can quickly generate professional looking, detailed reports by clicking-through a simple dialogue
Near real-time sensor data is available to security analyst
Encryption ensures privacy and integrity of collected data
Analysts can easily compare network activity over multiple locations and time spectrums
The system automatically represents multiple (often hundreds) detections of the same wireless device as a single entity
Improves the visibility of risks
Analysts can simply analyze large amounts of data
Allows analyst to efficiently navigate and focus on relevant threats
Enables analyst to examine threats using multidimensional tools
Immediate detection of anomalies and potential threats
Uncover organization risks for better decision making
Eases communication between an outdoor security vehicle and indoor analyst’s workstation
Benefits
Low capital expenditure to instrument a fleet or facility
Extends range of wireless security perimeter
Improves coverage of plant/facility by wireless sensors
Wireless collectors are less susceptible to physical vandalism
Leverages existing security force to help provide wireless security
Time under security coverage can increase from 3.5% to 50%1
Reduces recurring cost of wireless security patrols
Encodes organizational knowledge in system to increase continuity with staff turnover
Saves analyst time
Ease of generation encourages communication and sharing of information within team
Simplifies periodic security audits and on-going monitoring of external and internal networks
Reduces cycle time from detection, to identification, analysis, and response
Reduces capital expenditure through leverage of existing telecommunications infrastructure
Increases analyst comprehension
Saves analyst time by enabling him to quickly pinpoint areas of interest
Enables analysts to make more accurate assessments of a network’s security
Increases accuracy of an analyst’s evaluation
Gives an analyst a thorough understanding of all dependencies to wireless assets, therefore enabling him to make a complete and accurate examination of vulnerabilities
1 WildCAT provides a much greater degree of coverage than manual patrols. If we use our assumption that personnel currently have time conduct 2 hour manual patrols 3 times per week, this means that the “time under patrol” is only 6 hours per 168 hour week – only 3.5% of the time. Employing WildCAT would allow for 2 patrols to be run per shift, increasing the time under patrol to 84 hours – a much more comprehensive 50% of the time.