We are driven to provide users with advanced tools to enhance their security decisions, and to help them succeed wherever they need, from the developer’s workstation, to the corporate data center, or to the cyber battlefield.
That usually means solving problems that have never been approached before, and that is the core of our research and development activities.
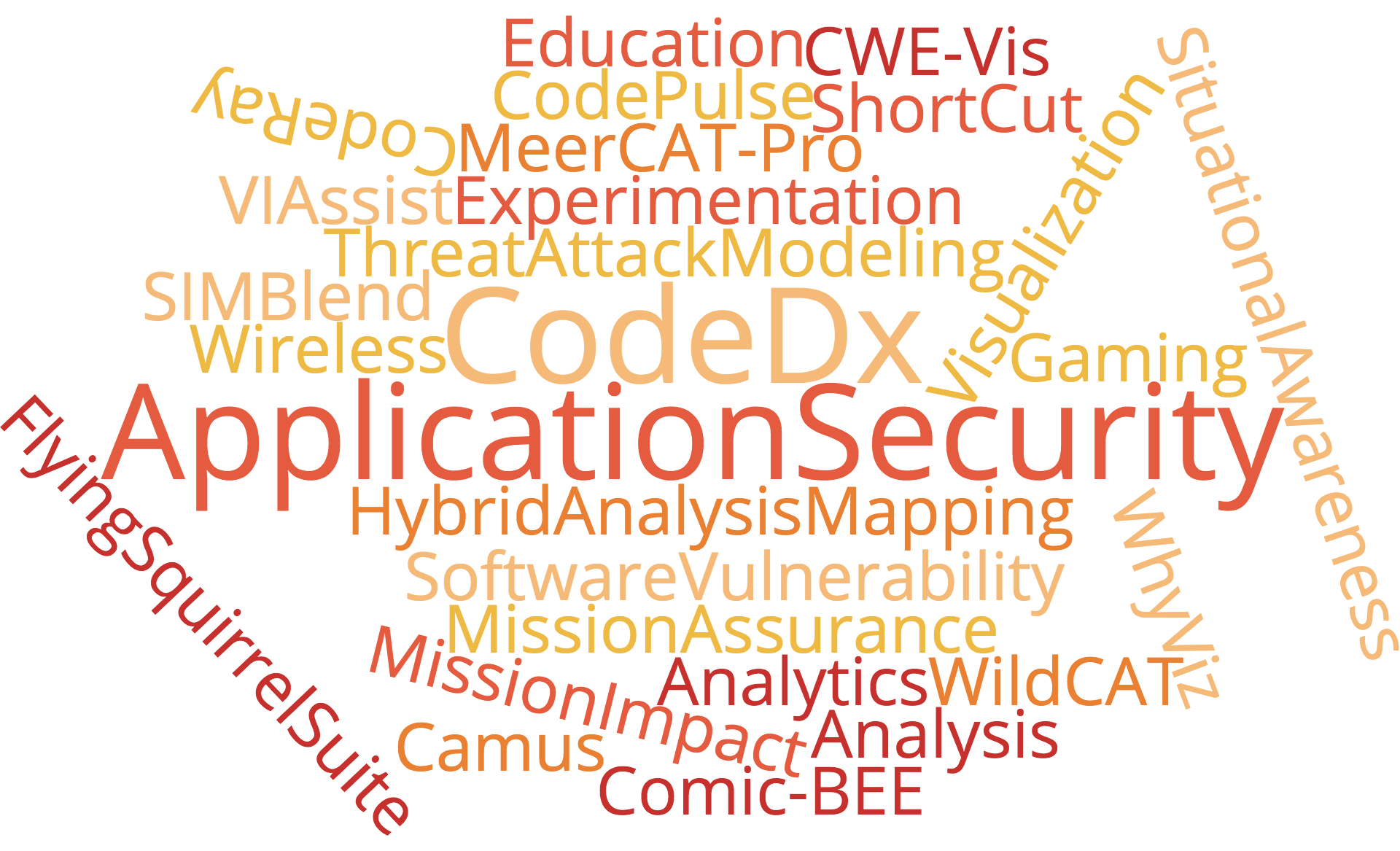
Our recent research includes:
Research areas
The focus of our research is to find new ways to take data and turn it into actionable information. Those responsible for network and infrastructure protection need to respond to events—especially threats—as they arrive, and speed is often critical. Unfortunately, sifting through mountains of data can be closer to finding a needle in a haystack. Through visualization techniques, threat modeling, analytics, and application security methods, we develop ways to quickly process that data and let the professionals do their jobs—or prevent the threats from becoming attacks in the first place.
End-user focus
Whatever problem domain we are addressing, our research is always focused on real users struggling with real-world problems. From corporate security offices to cyber warriors, our mission is to ensure that the work we do today will meet their needs and improve their effectiveness now—not ten years down the road. We achieve this by simply making them part of the entire process, from the very start through successful transition:
Technology transition
When we solve a problem, we don’t want the solution to gather dust; we aren’t in the business of making shelf-ware. After we have completed the R&D, we work diligently to transition the technology into operational use. This can mean commercialization, open-sourcing , or publishing the results so that the rest of the cyber community can benefit. We intend our projects to be used. We are currently partnered with Code Dx, Inc. to transition our application security R&D into commercial tools, and to maintain and update open source technologies (such as Code Pulse) developed by Secure Decisions.
We begin each research effort by developing a deep understanding of the needs, decisions, and work patterns of the people who will be the beneficiaries of our work. We achieve this through a formal process known as a Cognitive Task Analysis, or CTA.
We establish close relationships with end-users, and obtain their commitment to review and evaluate our technology as we develop it. Incremental releases are either informally evaluated or deployed into formal exercises, and results of those activities are fed back into the development cycle as early as possible.
- We are experienced in transitioning our technology into operational use, and we maintain a supportive relationship with our users post-transition to ensure they are realizing its full potential, and that it isn’t sitting on a shelf.


