Camus
Camus is a proof of concept that enables cyber impact assessment by modeling and automatically mapping cyber assets to the missions and users that depend on them.
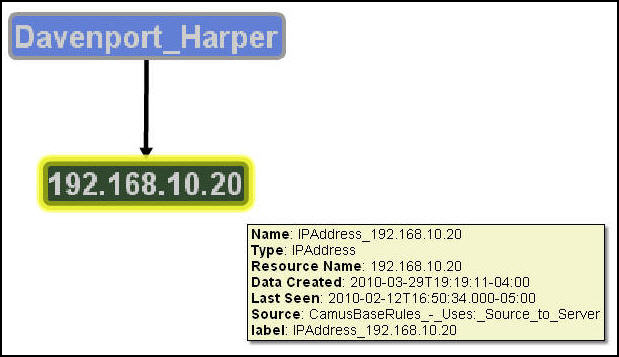
Camus collects from various sources data that describe the organization and the activity between users and cyber assets, such as traffic captures and people directories, and fuses the data into a comprehensive model that reveals relationships between cyber assets and the users and missions that rely on them. By automatically mining existing data to create contextual information, Camus provides an up-to-date picture of what an organization really looks like, who uses what asset, and what they are using it for. This information improves risk assessments by identifying critical assets and single points of failure for critical processes, and enhances situational awareness by providing an improved context for the decision-making process. Additionally, with no manual maintenance to update dependencies, and no client software install required, Camus saves time and labor.
Camus was funded by the Office of the Secretary of Defense, and managed by the Air Force Research Laboratory through a two-year Phase II Small Business Innovative Research contract that commenced in May 2008.
To learn more about Camus:
Mission-to-Cyber Mapping Ontology

Mission Impact Workshop
As part of the Camus project, Secure Decisions conducted a workshop on mapping cyber assets to missions and users. The workshop addressed how to map the relationships between cyber assets such as network devices and the users, missions, business processes and other entities that depend on those assets. The 30 participants included individuals with operational responsibility is to assure the availability of cyber assets for critical missions, researchers in areas related to the mapping of cyber assets to missions, and developers of technology that can be used in this mapping. The group exercises yielded insight into the information requirements for mapping cyber assets to missions and users, and the participant’s presentations summarized the state-of-the-art of this topic.

